Disabling Directory Browsing in the Main Configuration File
It’s simple to disable directory browsing in the Apache main configuration file by changing the Options directive to make sure the Indexes option is disabled. This directive determines how directories behave in a number of ways, such as whether directory browsing is permitted. By modifying the primary Apache configuration file, you can turn off directory browsing as follows:
- Depending on your operating system, the primary Apache configuration file is normally found in one of the following directories:
-
- Debian/Ubuntu
/etc/apache2/apache2.conf
-
- CentOS/RHEL
/etc/httpd/conf/httpd.conf
- Make a backup on the configuration file above by running the command below.
sudo cp -rp /etc/apache2/apache2.conf /etc/apache2/apache2.conf.backup
- Open the file and edit it with a text editor such as Vim or Nano.
nano /etc/apache2/apache2.conf
- Find the Directory Configuration Block. There are multiple blocks in the configuration file. These blocks specify configurations for particular server folders. The root directory is the highest-level directory on the server, and the settings in the block are applicable to it. Look for a block that is similar to the following:
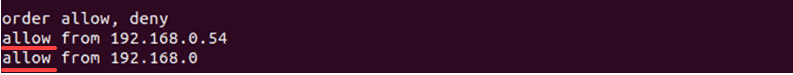
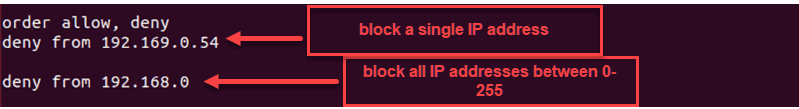
Within this block look for the line that contains Options (box in red). It may include the Indexes option, which enables directory browsing.
- Remove the Indexes option from the Options directive to disable the directory browsing. This is how the modified directive should appear.
- Save and exit on the editor. For changes to take effect, restart the Apache service. Run the command below.
-
- Debian/Ubuntu
sudo systemctl restart apache2
-
- Centos/RHEL
sudo systemctl restart httpd
- Verify that directory browsing has been disabled in order to validate the modifications. Then, use a web browser to access a directory on the server without an index file. Users should get a “403 Forbidden” response instead of a directory listing, indicating that directory browsing is no longer permitted.
Disabling Directory Browsing in Virtual Host Files
With Apache, different websites may be operated even on WordPress hosting; each with its own configuration, on a single server by using virtual hosts. One can change the configuration in the virtual host files to prevent directory browsing for particular websites or virtual hosts. Here’s how to make this happen:
- Depending on your operating system, the primary Apache configuration file is normally found in one of the following directories:
-
- Debian/Ubuntu
/etc/apache2/sites-available/
-
- CentOS/RHEL
/etc/httpd/conf.d/
or
/etc/httpd/sites-available/
- Every virtual host will have a configuration file of its own, usually called example.com.conf or after the domain or website it serves. Make a backup on the configuration file above by running the command below.
sudo cp /etc/apache2/sites-available/example.com.conf /etc/apache2/sites-available/example.com.conf.backup
- Open the file above and edit it with a text editor such as Vim or Nano.
nano /etc/apache2/sites-available/example.com.conf
- Find the Directory Configuration Block. There are multiple blocks in the configuration file. These blocks specify configurations for particular server folders. The root directory is the highest-level directory on the server, and the settings in the block are applicable to it. Look for a block that is similar to the following:
Within this block look for the line that contains Options (box in red). it may include the Indexes option, which enables directory browsing. - Remove the Indexes option from the Options directive to disable the directory browsing. This is how the modified directive should appear.
- Save and exit on the editor. For changes to take effect, restart the Apache service. Run the command below.
-
- Debian/Ubuntu
sudo systemctl restart apache2
-
- Centos/RHEL
sudo systemctl restart httpd
- Verify that directory browsing has been disabled in order to validate the modifications. Then, use a web browser to access a directory on the server without an index file. Users should get a “403 Forbidden” response instead of a directory listing, indicating that directory browsing is no longer permitted.
Disabling Directory Browsing Using .htaccess Files
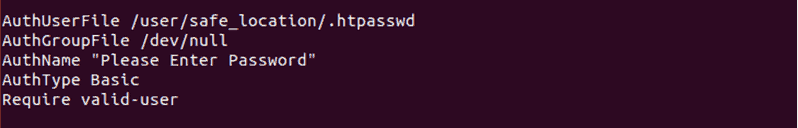
With Apache, the.htaccess file is a strong configuration tool that lets users change server settings for individual directories. One can change or create a.htaccess file in the directory where they wish to apply this setting if they don’t have access to the main Apache configuration file or if they want to block directory browsing for a particular directory. Using a.htaccess file, users can prevent directory browsing as follows:
- To disable directory browsing, navigate to the desired directory. This could be any subdirectory inside the site itself or the document root of the website (/var/www/example.com, for example).
cd /var/www/example.com
- If there’s already a .htaccess file in the directory, one can edit it with a text editor. Otherwise, one can make a fresh .htaccess file
sudo nano .htaccess
- Add the line below on the file then save and exit.
Options -Indexes
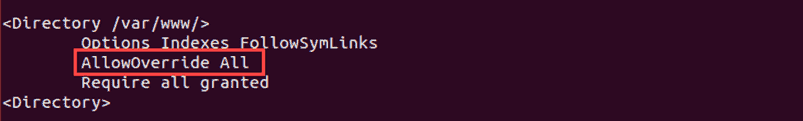
- Apache needs to be set up to permit .htaccess overrides in the appropriate directory in order for the .htaccess file to function. The AllowOverride directive in the virtual host or Apache configuration files controls this. Verify that the virtual host file or directory block in the Apache configuration permits overrides, as shown below.
- Verify that directory browsing has been disabled in order to validate the modifications. Then, use a web browser to access a directory on the server without an index file. Users should get a “403 Forbidden” response instead of a directory listing, indicating that directory browsing is no longer permitted.
Troubleshooting Common Issues
Although it is usually simple to disable directory browsing on Apache, there are certain issues that make the setup not work as intended. Users can solve typical problems while deactivating directory browsing on Apache by checking the list of solutions provided below.
- Directory browsing remains enabled even after making changes to the. htaccess file or Apache settings. To make the modifications take effect, make sure to restart the Apache server. Use the command that is right for your operating system.
-
- Debian/Ubuntu
sudo systemctl restart apache2
-
- CentOS/RHEL
sudo systemctl restart httpd
- Check to see if the Apache user is allowed to view the modified configuration files or the .htaccess file. These files may not be readable by Apache due to incorrect file permissions. Perform the following if issue has been encountered.
sudo chmod 644 /path/to/.htaccess
-
- Debian/Ubuntu
sudo chown www-data:www-data /path/to/.htaccess
-
- CentOS/RHEL
sudo chown apache:apache /path/to/.htaccess
- Users get a “403 Forbidden” error for all requests after disabling directory browsing, even when trying to access files that are supposed to be available. To enable Apache to serve files, make sure the directory permissions are set appropriately. Run the command to fix it.
sudo chmod 755 /var/www/example.com
- Make sure the AllowOverride directive in the Apache configuration is set to All, or at the very least, to allow the Options directive, especially if users are using a.htaccess file.
- After changing the configuration to deactivate directory browsing, Apache either fails to start or restarts with issues. Before restarting Apache, run a syntax check on the configuration files to identify any errors.
sudo apachectl configtest
- For more details on the reason why Apache is not starting, review the Apache error logs.
-
- Debian/Ubuntu
sudo tail -f /var/log/apache2/error.log
-
- CentOS/RHEL
sudo tail -f /var/log/httpd/error_log
CONCLUSION
One of the most important things one can do to secure the web server is to disable directory browsing on Apache. The directories’ contents can be kept hidden from unauthorized users, lowering the possibility of vulnerable information and sensitive data being exposed. Using.htaccess files, virtual host file adjustments, and changes to the main Apache configuration file are some of the methods available to stop directory browsing. There is flexibility in each option based on the server configuration and access level. Knowing how to limit directory browsing at different levels is important for those who oversee a single site or a number of virtual hosts. It guarantees that the server is safe and properly setup. Even though the procedure is normally simple, be ready to troubleshoot common problems to make sure the modifications are implemented correctly, such as wrong permissions, conflicting setups, or syntax errors. These actions will help to safeguard information, improve the security of the Apache server, and give users a safer environment. Maintaining a strong and secure online infrastructure includes routinely checking and updating the server’s settings, as well as turning off pointless functions like directory browsing.