As you’ll notice in Server 2008, there isn’t an option to backup the System State data through the normal backup utility.

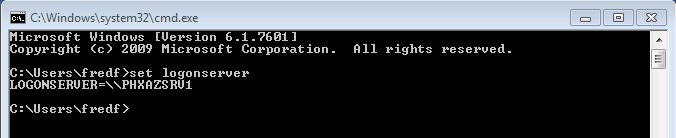
So what do we do? We need to go “command line” to backup Active Directory.
1. Open up your command prompt by clicking Start and type “cmd” and hit enter.
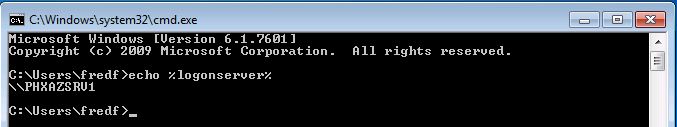
2. In your command prompt type “wbadmin start systemstatebackup -backuptarget:e:” and press enter.
Note: You can use a different backup target of your choosing
3. Type “y” and press enter to start the backup process.

When the backup is finished running you should get a message that the backup completed successfully. If it did not complete properly you will need to troubleshoot.

Now you have a system state backup of your 2008 Server!
Authoritative Restore of Active Directory
So now what if you accidentally delete an OU, group, or a user account and it’s already replicated to your other servers? We will need to perform an authoritative restore of the Active Directory object you accidentally deleted.
1. To do this you will need to boot into DSRM (Directory Services Restore Mode) by restarting your server and pressing F8 during the restart.
2.Choose Directory Services Restore Mode from the Advanced Boot menu.

3. Login to your server with your DSRM password you created during Active Directory installation.
4. Once you’re logged into your server and in DSRM safe mode, open a command prompt by clicking Start, type “cmd“, and press enter.
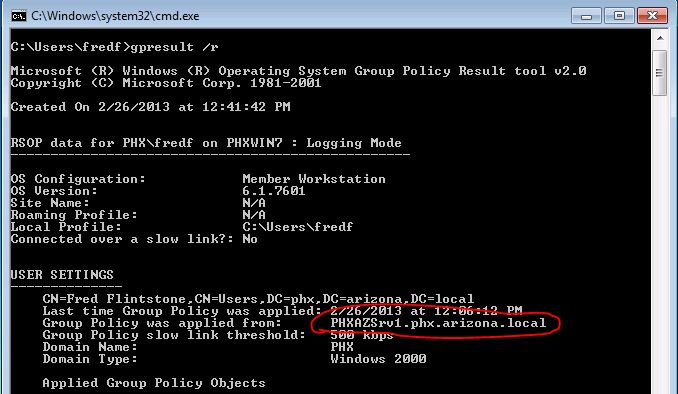
5. To make sure you restore the correct backup it’s a good idea to use the “wbadmin get versions” command and write down the version you need to use.

6. Now we need to perform a non-authoritative restore of Active Directory by typing “wbadmin start systemstaterecovery -version:04/14/2009-02:39“.
Note: The version of backup will vary depending on your situation. Type “y” and press enter to start the non authoritative restore.
7. Go grab some coffee and take a break while the restore completes.

8. You can mark the sysvol as authoritative by adding the –authsysvol switch to the end of the wbadmin command.